Web security refers to the practices and technologies used to protect websites, web applications, and data from cyber threats and unauthorized access.
- Protects data during transmission over the Internet.
- Safeguards websites, servers, users, and applications.
- Prevents data breaches, malware attacks, and hacking.
- Essential due to the increasing number of cyberattacks.
Major Cyber Threats Impacting Web Security
The internet is a powerful tool, but it also opens the door to serious security threats. From ransomware attacks to phishing scams, staying informed is the first step to staying protected.
- Ransomware
- SQL Injection
- Phishing
- Viruses and worms
- Spyware
- Cross-site scripting (XSS)
- Code Injection
- Denial of Service
Understanding Web Security
Web security is about keeping websites, servers, users, and devices safe from cyberattacks that come through the internet. These attacks can include things like viruses, fake emails (phishing), and other harmful activities that can steal or leak important information.
To stay protected, web security uses different tools and methods, such as firewalls, systems that block suspicious activity, filters that block dangerous websites, and antivirus software. It also covers the security of Web Apps, APIs, and cloud systems to keep everything running safely online.
Example: When you are transferring data between client and web server and you have to protect that data, that security of data is your web security.
Latest Trends in Web Security
In today’s digital world, web security is becoming increasingly important as cyber threats grow more advanced and frequent. Attacks like phishing, ransomware, and IoT-based threats can cause serious financial, reputational, and legal damage. To stay secure, organizations and individuals must adopt modern security practices and technologies to protect data and ensure safe operations.
- Cyber threats are increasing in complexity and frequency
- Attacks can cause financial, reputational, and legal damage
- Advanced technologies are required for protection
- Strong access controls help prevent unauthorized access
- Secure development practices ensure safer applications
Key Trends in Web Security
1. AI and Machine Learning in Cybersecurity
Artificial Intelligence (AI) and Machine Learning (ML) are transforming cybersecurity by enabling real-time threat detection and automated response. These technologies analyze large volumes of data to identify unusual patterns and predict potential attacks before they occur.
2. Zero Trust Security Model
The Zero Trust model operates on the principle of “never trust, always verify.” Every user, device, and application must be authenticated and authorized before access is granted, reducing the risk of unauthorized access and insider threats.
3. Secure DevOps (DevSecOps)
DevSecOps integrates security into every stage of the software development lifecycle. By embedding security early in the process, organizations can identify and fix vulnerabilities faster, reducing the risk of exploitation after deployment.
4. IoT Security
With the rapid growth of Internet of Things (IoT) devices, securing connected systems has become essential. Proper IoT security measures help prevent devices from becoming entry points for cyberattacks and protect the overall network infrastructure.
Top Web Security Tools for Developers and Security Experts
To effectively protect web applications, it’s important to use the right tools and resources. These tools help identify security issues, defend against attacks, and improve overall system safety. Whether you're a developer, tester, or security professional, the following resources can support strong web security practices.
- OWASP ZAP: A free, open-source tool used to find security flaws in web applications.
- Burp Suite: A powerful platform for analyzing and testing web application security.
- Cloudflare: Offers protection against DDoS attacks and enhances performance with CDN services.
- SSL Labs: Evaluates the security of your SSL/TLS setup and provides a detailed report.
- Snyk: Detects vulnerabilities in open-source libraries and helps fix them quickly.
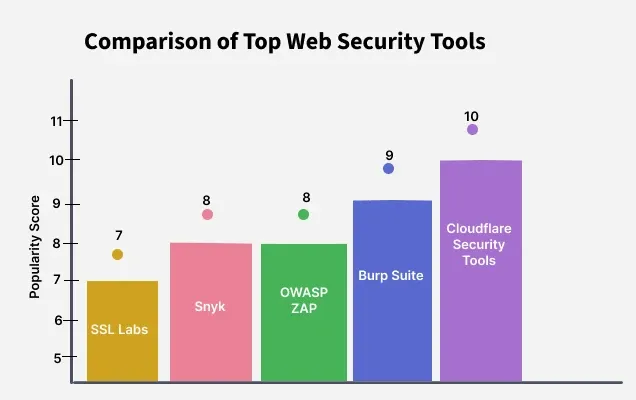
Note: Cloudflare is the best, with a top score of 10, meaning it gives the strongest protection. Burp Suite is also very good with a score of 9. OWASP ZAP and Snyk both scored 8, showing they are also strong tools. SSL Labs has the lowest score of 7, so it may not be as powerful as the others.
Best Practices for Securing Your Website
- Keep Software Updated: Regularly update all software to fix known vulnerabilities and prevent exploits by hackers.
- Beware of SQL Injection: Prevent attackers from injecting malicious queries into your database by using parameterized queries and input validation.
- Prevent Cross-Site Scripting (XSS): Sanitize user input to block scripts that could run in users’ browsers and steal sensitive data.
- Limit Error Messages: Avoid exposing system details in error messages. Keep messages generic to prevent attackers from gaining insight.
- Validate User Input: Perform input validation on both client and server sides to block malformed or malicious data.
- Use Strong Passwords: Enforce complex password policies to protect against brute-force attacks include uppercase, lowercase, numbers, and symbols.
- Implement HTTPS: Secure your website with HTTPS to encrypt data during transmission and prevent interception.
- Enable Two-Factor Authentication (2FA): Add an extra layer of security by requiring a second form of verification beyond a password.
- Access Control: Restrict access based on user roles and use the principle of least privilege to minimize risk.
- Monitor and Log Activity: Keep logs of access and actions on your site to detect suspicious behavior and audit breaches.
- Use Modern and Secure Tech Stacks: Build websites using updated and secure frameworks like the MEAN stack (MongoDB, Express.js, Angular,Node.js) for better performance, scalability, and built-in security features.

Comments
Post a Comment